Security operations have moved far beyond monitoring isolated alerts. For modern enterprises, the challenge is no longer a lack of security signals, but the ability to rapidly classify, prioritize, and respond to incidents across a fragmented security stack. When SIEM alerts, endpoint telemetry, cloud logs, identity events, and threat intelligence remain siloed, SOC teams lose critical context, response slows, and analyst fatigue grows.
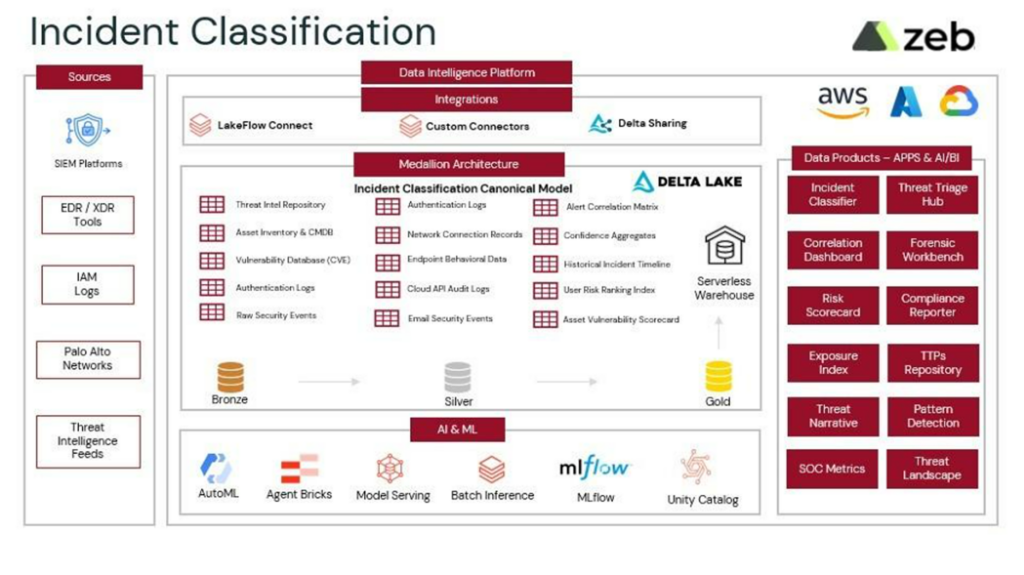
The Databricks App for Incident Classification & Threat Intelligence addresses this challenge by delivering a real-time, AI-assisted workspace for SOC leaders and CISOs. Built on the Databricks Data Intelligence Platform, it unifies security telemetry into a governed Security Lakehouse and applies ML-driven classification, correlation, and conversational analytics to accelerate response while preserving auditability and compliance.
Unifying security signals into a trusted incident foundation
The application ingests high-volume security telemetry from SIEM, EDR, cloud, identity, firewall, and threat-intelligence sources through a structured, streaming intake layer. Events are validated and stored as immutable Bronze Delta tables, ensuring forensic integrity and traceability from the moment data lands.
As data flows into Silver, Databricks pipelines normalize schemas, resolve entities, enrich events with threat context, and engineer features for classification models. Curated Gold views publish incident, asset, and user-risk datasets optimized for real-time analytics, investigation, and reporting.
With Unity Catalog enforcing centralized governance, fine-grained access control, lineage, and audit logging, security teams operate on a single, compliant foundation that supports SOC 2, HIPAA, and PCI-DSS requirements without sacrificing speed or flexibility.
Real-time incident classification at operational scale
At the core of the solution is a real-time incident classification engine that transforms raw alerts into prioritized, high-confidence incidents within seconds. A unified triage dashboard presents incidents by type, severity, confidence score, affected asset or user, detection source, and recommended response.
SOC leaders gain immediate visibility into:
- Malware, credential abuse, lateral movement, exfiltration, and anomalous activity
- Classification latency and confidence indicators
- Geospatial context for affected assets and attacker origins
- Inline response and escalation guidance aligned to playbooks
By correlating activity across tools and mapping events to the MITRE ATT&CK framework, the platform reveals full attack chains instead of isolated signals, enabling analysts to act decisively rather than investigate blindly.
Deep forensic context with correlated timelines
Each incident includes a detailed forensic view that stitches together activity across endpoints, identities, networks, and cloud services. Analysts can explore correlated timelines, lateral movement paths, similar historical incidents, and trend patterns across 24-hour and 7-day windows.
Because all metrics refresh in near real time, SOC teams maintain continuous situational awareness as incidents evolve, without waiting on batch reports or manual correlation.
Conversational threat intelligence for faster decisions
The built-in Security Analyst Assistant (Genie) enables natural-language interaction with governed security data. Analysts and leaders can ask questions such as:
- “Which critical incidents are impacting customer-facing systems today?”
- “Which users show the highest risk based on login anomalies?”
- “Which incidents have remained open for more than 30 minutes?”
Responses include clear answers, confidence indicators, and direct links to dashboards, raw events, and recommended actions, turning investigation into a guided, self-service experience rather than a manual search exercise.
Controlled automation with full auditability
SOC leaders can tune classification models directly through a governed interface, adjusting thresholds, confidence cutoffs, and feature weights with mandatory previews against historical incidents. All models are versioned through MLflow and Unity Catalog, enabling rollback and full audit traceability.
Automated response triggers such as escalations, tickets, notifications, or SOAR integrations can be defined based on incident severity. Every configuration change and execution is logged, approved, and auditable, ensuring automation strengthens security posture without introducing risk.
Strategic visibility for executive leadership
For CISOs, the platform delivers an aggregated, executive-level view of enterprise security posture. A unified scorecard surfaces KPIs such as incident volume by severity, mean time to classify, backlog trends, false-positive rates, and team utilization tracked across 30- and 90-day windows.
Risk ranking dashboards highlight the most vulnerable assets and users based on exposure, behavior, and incident history, while threat-landscape views connect internal incidents to external campaigns and regulatory control impacts.
Through the CISO advisory assistant, leaders can explore trends, ROI scenarios, and compliance posture using conversational queries and exportable summaries without relying on manually assembled SOC reports.
What sets this solution apart
The Databricks App for Incident Classification & Threat Intelligence is purpose-built for modern SOC and executive workflows. Its differentiators include:
- A unified, governed Security Lakehouse across all telemetry sources
- ML-driven incident classification that prioritizes high-risk threats and reduces noise
- Real-time streaming pipelines that keep metrics fresh within seconds
- Conversational analytics for both technical and non-technical stakeholders
- Built-in lineage, immutability, and audit trails for regulatory compliance
Measurable outcomes from AI-driven classification
Organizations adopting this approach have achieved tangible improvements across security operations:
- Mean time to detect and classify reduced from 45–60 minutes to under 2 minutes
- False positives reduced by 65–75%, significantly lowering analyst fatigue
- Security team productivity increased by 40–50%
- Incident handling costs reduced by 30–40%, enabling greater focus on proactive threat hunting
From alert overload to intelligent response
By unifying fragmented security signals, applying ML-driven classification, and enabling conversational threat intelligence on a governed platform, the Databricks Security Lakehouse transforms how organizations detect, understand, and respond to incidents.
As a trusted Databricks partner, zeb helps enterprises modernize security operations with scalable, AI-driven foundations that deliver faster response, stronger governance, and clearer risk visibility today and threat landscapes continue to evolve.