Security operations teams today face a growing paradox. While security telemetry has never been richer, the ability to turn that data into timely, actionable insight remains limited. Alert volumes continue to rise; attacks increasingly span identity, endpoints, networks, and cloud platforms, and investigations still rely heavily on manual correlation across fragmented tools.
At zeb, this challenge appears consistently across industries and security maturity levels. The issue is not a lack of detection technologies, but the absence of a unified, governed platform that can correlate signals, apply intelligence at scale, and support both analysts and executives effectively. This is where AI-assisted SIEM augmentation using the Databricks Data Intelligence Platform fundamentally changes how security operations function.
Why traditional SIEM-Centric Approaches fall short
SIEM platforms remain central to most SOCs, yet they were not designed to serve as the single system of record for modern security operations. As organizations introduced EDR, identity providers, cloud security tools, and threat intelligence platforms, security data became distributed across systems that do not naturally correlate.
Analysts often pivot between multiple consoles, export logs into spreadsheets, and manually reconstruct attack timelines. Rule-based correlation struggles to keep pace with identity-driven and multi-stage attacks, while alert fatigue erodes trust in detection quality. Even when alerts are triggered quickly, understanding the full scope, intent, and business impact of an incident frequently takes too long.
The result is a SOC that reacts to alerts instead of operating with continuous situational awareness.
Augmenting SIEM with a unified security lakehouse
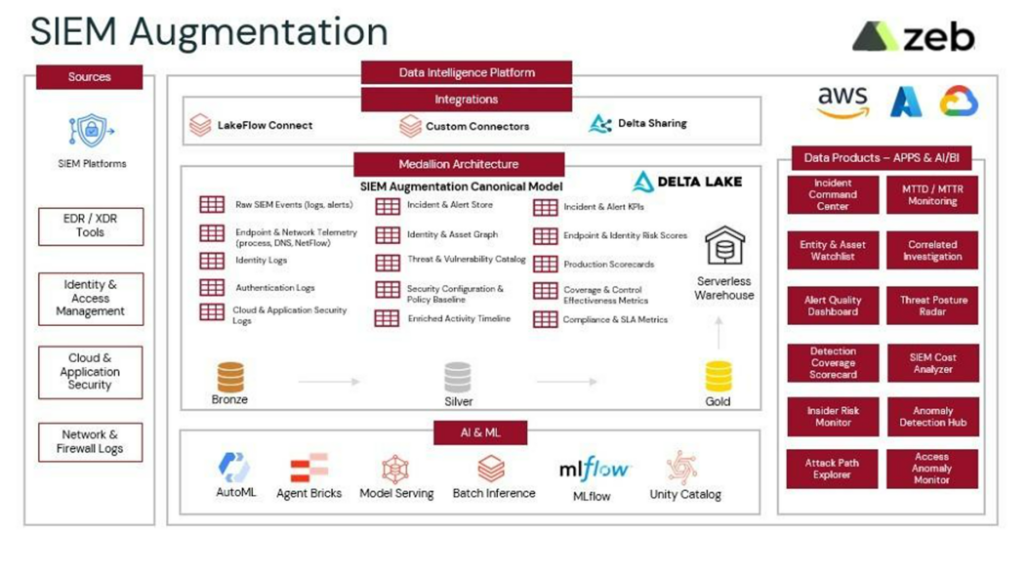
Rather than replacing existing SIEM investments, zeb focuses on augmenting SIEM with a unified security data layer built on the Databricks Lakehouse. All security telemetry alerts, raw logs, identity signals, network flows, cloud audit data, and case history is consolidated into a single governed platform optimized for analytics and AI-assisted investigation.
Security data is organized using a medallion architecture. Raw telemetry lands in the Bronze layer, enriched and normalized data is curated in Silver, and investigation-ready incident views and UEBA risk signals are published in Gold. This structure enables scalable correlation, consistent enrichment, and reliable analytics across the entire security estate.
By unifying telemetry at the data layer, correlations that were previously manual or brittle become continuous and repeatable without disrupting existing SOC tools or workflows.
Transforming SOC operations with AI-assisted investigation
Once security data is unified, the analyst experience changes fundamentally. Event ingestion and triage are no longer opaque background processes, but observable pipelines with clear visibility into ingestion health, latency, and data quality. Analysts can trust that enrichment, normalization, and correlation have completed before beginning an investigation.
Incident investigation itself shifts from alert review to attack understanding. Analysts work from a single investigation dashboard that correlates signals across SIEM, EDR, identity, and network telemetry. Attack timelines show how incidents unfold from initial access to impact, while enriched context highlights affected users, assets, applications, and historical patterns.
Instead of manually pivoting between tools, investigators are presented with complete attack chains and supporting evidence by default, enabling faster and more confident response decisions.
Behavioral analytics and continuous risk scoring
Behavioral analytics form the backbone of prioritization in modern SOCs. Rather than treating every alert equally, the platform continuously evaluates user, asset, and application behavior against historical baselines.
Risk scores evolve in near real time as new events arrive, capturing signals such as abnormal authentication activity, privilege escalation, lateral movement, and anomalous data access. This dynamic scoring model helps SOC teams focus investigations where risk and business impact intersect, reducing noise while improving response effectiveness.
Conversational threat hunting with governed AI
Databricks AI/Genie introduces a conversational layer that makes threat hunting more accessible without compromising governance. Analysts can ask natural-language questions and receive governed, auditable responses backed by curated security datasets.
Examples include:
- Identifying users with abnormal login behavior in the past 24 hours
- Summarizing incidents associated with a specific IP or device
- Detecting assets exhibiting lateral movement patterns
Queries remain fully traceable, with source attribution and preserved context for follow-up questions. This allows SOC teams to democratize threat hunting while maintaining investigation integrity and compliance.
Executive visibility without operational noise
For CISOs and security leadership, visibility must be comprehensive, accurate, and controlled. The executive security posture dashboard aggregates operational signals into metrics that reflect detection effectiveness, response efficiency, and overall risk exposure.
Leadership teams gain near real-time insight into MTTD, MTTR, detection coverage, alert quality, incident trends, and compliance posture across business units and geographies. Because access is governed through Unity Catalog and role-based controls, executives can explore insights directly without introducing audit or data-exposure risk.
This bridges the gap between SOC operations and strategic security decision-making.
Extending the platform for threat intelligence teams
Threat intelligence teams benefit from the same unified Lakehouse foundation. Incidents and tactics can be clustered into evolving threat actor profiles, mapped to MITRE ATT&CK techniques, and enriched with external intelligence feeds.
The platform supports controlled publishing of threat reports, IOC feeds, and STIX/TAXII exports, with full versioning and audit logging. This enables organizations to operationalize threat intelligence while maintaining strong governance over sensitive data.
Governance, compliance, and auditability by design
Security analytics are only valuable if they are trusted. The Databricks Lakehouse enforces governance as a core capability:
- Unity Catalog provides centralized access control, lineage, and auditing
- Row- and column-level security protects sensitive data
- Delta Lake ensures immutable, ACID-compliant audit trails
- AI-assisted investigations remain governed and traceable
This makes the platform suitable not only for detection and response, but also for compliance reporting and forensic investigations.
Measurable outcomes for security operations
Organizations adopting this SIEM augmentation approach typically achieve:
- 30–50% reduction in MTTD and MTTR through automated correlation
- 2–3× improvement in alert quality through normalization and enrichment
- Lower SIEM ingestion and retention costs by offloading heavy analytics
- Faster triage and fewer escalations, improving analyst efficiency
Most importantly, security teams gain clarity that they are operating from a complete, accurate view of their threat landscape.
How zeb can help
zeb helps organizations modernize security operations by augmenting existing SIEM platforms with governed, AI-assisted analytics on Databricks. Our security and data specialists work closely with SOC teams and CISOs to design, build, and operationalize unified security Lakehouses that enable faster investigations, better risk prioritization, and executive-ready visibility.
If your security operations are constrained by fragmented telemetry, alert fatigue, or slow investigations, zeb can help assess your current SIEM architecture and define a practical path toward AI-assisted security operations on Databricks.
Talk to zeb about SIEM augmentation and security analytics modernization.